Support for DSpace 5 ended on January 1, 2023. See Support for DSpace 5 and 6 is ending in 2023 |
DSpace 5.1 can be downloaded immediately from: More information on the 5.1 release (and the 5.x platform in general) can be found in the 5.x Release Notes. |
DSpace 5.1 contains security fixes for both the XMLUI and JSPUI. To ensure your 5.x site is secure, we highly recommend all DSpace 5.x users upgrade to DSpace 5.1. We also highly recommend removing any "allowLinking=true" settings from your Tomcat's <Context> configuration. Previously our installation documentation erroneously listed examples which included "allowLinking=true", while the Tomcat documentation lists it as a possible security concern. The XMLUI Directory Traversal Vulnerability (see below) is also exacerbated by this setting. |
If you are running an older, unsupported version of DSpace (1.x.x), we highly recommend upgrading to DSpace 3.4, DSpace 4.3 or DSpace 5.1 to ensure your site is secure. Several of these security vulnerabilities also affect sites which are running DSpace 1.x.x releases. Per our DSpace Software Support Policy, all DSpace 1.x.x versions are now End-Of-Life. If you are considering an upgrade from DSpace 1.x.x, note that, as of DSpace 5, your existing data (i.e. database contents, search/browse indexes) will now be automatically upgraded from ANY prior version of DSpace. Therefore, you may wish to consider upgrading directly to DSpace 5.1, as the 5.x upgrade process is simplified. |
DSpace 5.1 is a security and bug fix release to resolve several issues located in DSpace 5.0. As it only provides only bug fixes, DSpace 5.1 should constitute an easy upgrade from DSpace 5.0 for most users. No database changes or additional configuration changes should be necessary when upgrading from DSpace 5.0 to 5.1.
This release addresses the following security issues discovered in DSpace 5.x and below:
[HIGH SEVERITY] XMLUI Directory Traversal Vulnerabilities (DS-2445 - requires a JIRA account to access for two weeks, and then will be public): These vulnerabilities allow someone to potentially access any file on your local filesystem which is readable to the Tomcat user account. This includes files which are unrelated to DSpace or Tomcat, but are readable to all users on the filesystem (e.g. /etc/passwd, /etc/hosts, etc.). This also includes Tomcat configuration files (which may or may not contain passwords). These vulnerabilities have existed since DSpace 1.5.2.
Discovered by: Khalil Shreateh, with additional (related) vulnerabilities discovered by the DSpace Committer Team
In addition, this release fixes a variety of minor bugs in the 5.0 release. For more information, see the Changes section below.
5.1 is a bug-fix / security-fix release. This means it includes no new features and only includes the above listed security fixes For a list of all new 5.x Features, please visit the 5.x Release Notes. |
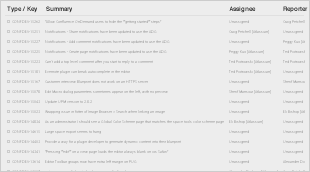
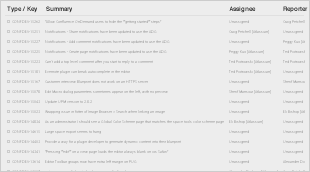
The following security fixes were released in 5.1. All of these tickets require a valid JIRA account to view the details:
The following bug fixes were released in 5.1.
Release Timeline: